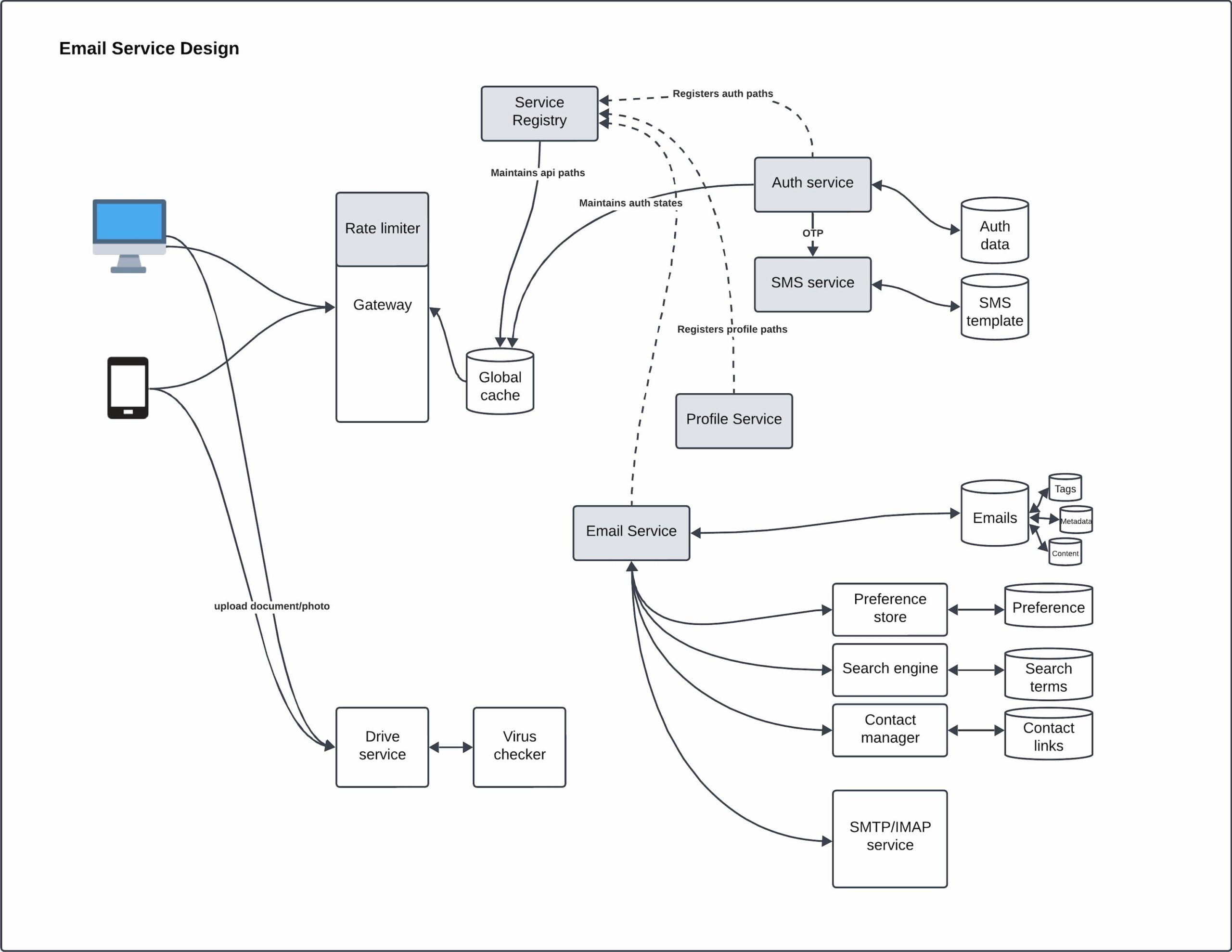
In this blog, we’ll explore how to design a scalable and efficient email service by breaking down each component of the system. Below is a diagram of our email service design, which highlights various modules, interactions, and data flows, providing a complete picture of how an email service works under the hood.
User Interaction and Input Handling
At the very beginning of the flow, users interact with the email service through devices like computers or smartphones. They can compose emails, send messages, and upload files, such as documents or photos. Uploaded files are immediately passed to a Virus Checker to ensure security. If the file is safe, it is sent to the Drive Service, where it is stored. This provides a secure storage layer for attachments and files, avoiding malicious content being spread.
Rate Limiter and Gateway for Controlled Access
After the user initiates a request (such as sending an email), it passes through the Gateway. The Gateway is the entry point for all requests to the system, ensuring routing to the appropriate services.
Attached to the Gateway is the Rate Limiter. The Rate Limiter helps control the volume of requests coming from each user, ensuring that no single user can overwhelm the system with excessive requests (e.g., due to a denial-of-service attack or accidental flooding). This helps maintain the service’s reliability and protects against misuse.
Global Cache and Service Registry
Once the request passes the gateway, it accesses the Service Registry. The Service Registry acts as a directory, maintaining the list of available services (such as the Auth Service, Profile Service, etc.) and their respective paths. This ensures that requests are routed to the correct service efficiently.
In addition to the Service Registry, the Global Cache stores frequently accessed data such as user sessions, authentication tokens, and user preferences. By caching this information, we significantly improve the system’s response time and reduce the load on the backend services.
Authentication and Profile Services
- Auth Service: To ensure secure access, the Auth Service manages user authentication. If additional security is needed, the SMS Service handles two-factor authentication (2FA) by sending a One-Time Password (OTP) to the user. This helps prevent unauthorized access and provides an extra security layer.
- Profile Service: Once authenticated, the Profile Service manages and provides user-specific information, such as preferences and profile details. This personalization ensures a customized and seamless experience for each user.
Core Email Service and Components
The central component of this architecture is the Email Service. It serves as the heart of the system, managing all email-related operations. Let’s look at the related services that support the Email Service:
- Preference Store: The Preference Store manages user settings and preferences, such as email notification preferences, spam filtering, and folder customizations. By maintaining these settings separately, the email service can efficiently retrieve and apply them to enhance user experience.
- Search Engine: Users often need to find specific emails quickly. The Search Engine indexes all incoming and outgoing emails using various metadata and search terms (such as subject, sender, or tags). It provides fast and accurate search capabilities across large volumes of data.
- Contact Manager: The Contact Manager is responsible for managing a user’s contact list. This can keep the mappings between the emails that become contact of each other after an email transaction.
- Emails Database: The actual emails are stored in a dedicated Emails Database. Each email contains multiple components, including metadata (such as timestamps and sender/receiver information), tags (for easy categorization), and the content (the body of the email). Efficient storage and retrieval of these components are crucial for ensuring smooth email operations.
SMTP/IMAP Services for External Communication
To interact with external email clients, the system uses SMTP (Simple Mail Transfer Protocol) and IMAP (Internet Message Access Protocol) services. These protocols allow the email service to send emails to other domains (via SMTP) and retrieve emails from external servers (via IMAP). This enables compatibility with widely used email clients, ensuring that users can seamlessly send and receive messages from various platforms. Once the local services are done, SMTP allows to send the email to appropriate mail receiver.
Key Considerations for Designing an Email Service
- Scalability: Email systems need to handle a massive number of requests, especially for popular services with millions of users. Components like the Rate Limiter, Global Cache, and Service Registry help maintain performance under high loads.
- Security: Handling sensitive information like emails requires robust security measures. The integration of Virus Checker, Auth Service, and SMS Service ensures that the data remains safe and that unauthorized access is prevented.
Conclusion
The above email service design demonstrates how various components interact with each other to provide a robust and efficient email solution. From user interaction, security checks, and rate limiting to the management of emails, contacts, and preferences—each module plays a critical role in the smooth functioning of the service. Understanding these components and their interactions is essential for designing scalable, secure, and user-friendly email systems.
With this design approach, you can build an email service that not only meets user expectations but also ensures security and scalability.



